The EU’s General Data Protection Regulation (GDPR) is set to go into effect in May 2018 triggering penalties for non-compliance with the new set of rules. As IT departments rush to ensure that everything is ready for the change, one key area is being overlooked according to some experts - Access Control.
“Most IT departments are forgetting about the access control database because it is owned by security,” said Andrew Bull, Director of Sales for UK&I, Quantum Secure. Bull has sent out a warning to address the issue or pay the price. “GDPR has put teeth in the data protection act and, for once, a regulation could hurt if a company doesn’t pay attention,” said Bull.
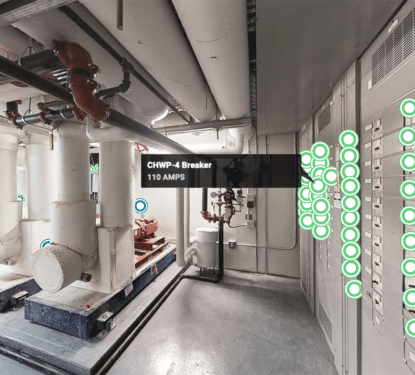
Physical security is being driven by IP enabled devices and the smart building movement. The total value of Physical Security products at factory gate prices in 2017 was $29.2Bn, an increase of approximately 5% on 2016, with Access Control taking a large share with 23.5% according to our latest report – The Physical Security Business 2017 to 2022.
The IoT and our digital society in general had brought the data privacy issue to the fore; after four years of preparation and debate the GDPR was finally approved by the EU Parliament on 14 April 2016. It will enter in force 20 days after its publication in the EU Official Journal and will be directly application in all members states two years after this date. Enforcement date: 25 May 2018 - at which time those organizations in non-compliance will face heavy fines.
The new regulation will carry an impact well beyond the EU however. Firstly, the UK, soon to exit the EU was involved in drafting the act and is on track for compliance. Further afield, a recent PwC pulse survey found that over half of US multinationals have GDPR readiness as their top data-protection priority. Guided by principles such as data protection by design and by default, the GDPR will force organizations to rethink their security practices.
The GDPR replaces the Data Protection Directive 95/46/EC in the EU and was designed to harmonize data privacy laws across Europe, to protect and empower all citizens data privacy and to reshape the way organizations across the region approach data privacy. Six months between its release and its enforcement and companies do not seem clear on what exactly they need to do, especially in the case of access control.
The 88 page legislative act often leaves room for interpretation with phrases like “appropriate technical and organisational measures” throughout the paper. In regard to hacking for example, the document (recital 49) also highlights the need for IT networks secure enough to resist “accidental events or unlawful or malicious actions” that may compromise the confidentiality of stored or transmitted personal data, and “the security of the related services offered by, or accessible via, those networks and systems.”

The cyber security section puts question marks over how realistic enforcement “to the letter” would be, most would agree that hacking is impossible to stop, but this is less often the case in data privacy. In both cases enforcement would probably only go as far as ensuring organizations are doing what they would reasonably be expected to do. With this in mind Bull summarized the key points of the GDPR for the access control problem in an article for IFSEC:
Consent: An organisation should have a specific statement in which an employee gives their consent about the data being held in the physical access system database. This should not be presumed consent.
Policy: An organisation needs to define the purpose of keeping data. If an employee leaves a company, when do you delete their information? Is there a legitimate reason to keep the data?
Process assurance: An organisation needs to define who has access to the database and also be able to track where the data is stored. Article 33 of GDPR says a company needs to report a personal data breach within 72 hours of the breach and report who is affected.
Contractors and visitors: There needs to be a policy and consent form for contractors and visitors. We rarely ask for consent for visitors but organisations should add a check-in box so a visitor understands their data is being stored on the database and a clear statement about what is being done with the data.
There is no insurmountable point here, but without the proper protocols being put in place and held up, organizations cannot count on leniency and may end up with heavy penalties. That is the fear with access control data, its isolation in the security department may mean it goes under the radar. Bull has some advice for organizations who worry they might be in danger of such as situation.
“Talk to your legal team. The legislation is not written with access control in mind and reading the documents can be tedious,” said Bull. “Get your legal team involved to help plan for the regulation.”
[contact-form-7 id="3204" title="memoori-newsletter"]